- Cybersecurity, Deterministic Computing
How DAIOS Is Rewriting Cybersecurity Entirely
Cybersecurity exists because machines are allowed to change state without permission.
Every firewall, SOC, intrusion-detection system, and incident-response playbook assumes the same thing: a system will execute first, break second, and be analyzed later. Security, in this model, is the art of managing damage after an invalid state already exists.
That approach worked when systems were slow, human-paced, and loosely coupled. It collapses the moment machines operate autonomously.
DAIOS starts from a different premise. A machine should not be allowed to change state unless that transition is provably admissible under deterministic law. If the state cannot be proven lawful, safe, and valid, it does not occur. There is no exploit to detect, no breach to respond to, and no incident to investigate.
This is not better monitoring. It is the removal of state corruption as a possibility.
Once authority is enforced at the state-transition level, cybersecurity stops being a discipline and becomes an artifact of outdated architecture.
That is what DAIOS changes and why cybersecurity, as we know it, does not survive it.
What Is DAIOS and Why Authority Matters
in Cybersecurity
DAIOS is not a security product, a monitoring layer, or an AI model. It is a deterministic operating system kernel designed to decide whether a machine is allowed to change state at all.
In conventional systems, authority is assumed. If code runs, the system treats the resulting state as legitimate and relies on cybersecurity tools to catch problems afterward. That means authority is implicit, optional, and always late.
DAIOS makes authority explicit and mandatory. Every proposed state transition is evaluated under deterministic rules and ethical constraints before execution occurs. If a transition cannot be proven admissible, it is not delayed, sandboxed, or logged. It is refused.
This is why authority matters in cybersecurity. Attacks, exploits, and breaches are not events. They are illegal state transitions. When a system cannot enter an illegal state, there is nothing left to secure.
Cybersecurity tries to manage systems that are already allowed to misbehave.
DAIOS removes that permission entirely.

Why Cybersecurity Exists:
Machines Are Allowed to Change State
Cybersecurity exists for a simple reason: machines are allowed to change state without explicit permission.
Modern systems assume that if code executes, the resulting state is valid by default. Only afterward do we inspect logs, scan memory, flag anomalies, or trigger alerts. By the time security becomes involved, the system has already accepted the change as real.
Every exploit depends on this ordering. Attacks don’t usually force their way in. They work by presenting state changes the machine is willing to accept, even when those states are unsafe, unintended, or malicious.
Firewalls, detection engines, and response teams are built to manage the aftermath. They observe, analyze, and respond, but they do not decide whether a state change should have been allowed in the first place.
Cybersecurity is not proof of control.
It is proof that control arrives after the moment that mattered.
Why Cybersecurity Fails:
Monitoring After State Change
Cybersecurity breaks for a simple reason: it shows up after the system has already moved.
Most security tools are built to watch, log, and react. A process runs. A state changes. Then the alerts fire, the dashboards light up, and the investigation begins. By definition, security enters the story late.
That timing used to be acceptable. Systems were slower. Decisions were reversible. Humans could step in. Today, machines operate at speeds where execution and consequence are effectively the same moment.
Once a system accepts a bad state, everything that follows is damage control. Monitoring can explain what happened. It can’t undo the fact that it happened.
That’s the uncomfortable truth underneath modern cybersecurity: it doesn’t govern behavior. It narrates the aftermath.
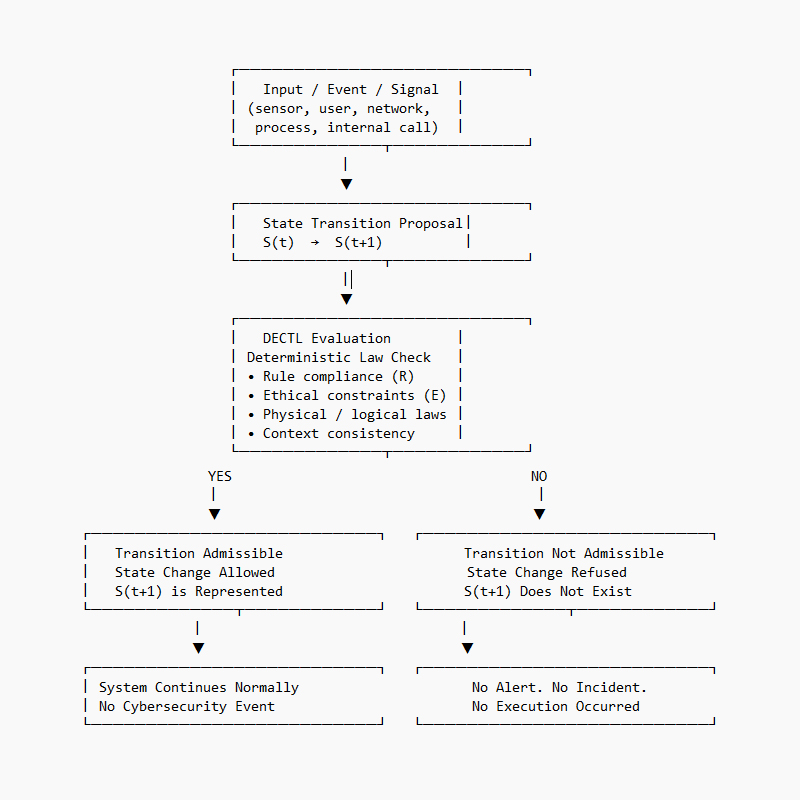
DAIOS and DECTL:
Cybersecurity at the State-Transition Level
DAIOS approaches cybersecurity from a place most systems never reach: the moment before a machine changes state.
In conventional architectures, inputs arrive, code executes, and the system moves forward. Security tools watch from the outside, logging what happened and deciding whether it looks suspicious. By the time an alert is raised, the state already exists. The system has accepted it as real.
DAIOS reverses that order.
Under the Deterministic Ethics-Constrained State Transition Law, every action is treated as a proposal, not an instruction. Inputs from sensors, users, networks, or internal processes do not directly cause execution. They propose a transition from the current state to a new one.
That proposed transition is then evaluated deterministically. The system checks whether the next state complies with defined rules, ethical constraints, physical limits, and contextual consistency. There is no scoring, no probability, no confidence threshold. The transition is either admissible or it is not.
If it is admissible, execution proceeds.
If it is not, execution never occurs.
This is the critical distinction. In DAIOS, cybersecurity is not a reaction to bad behavior. It is the absence of bad behavior as a representable outcome. An exploit does not fail because it is detected. It fails because the state it depends on is never allowed to exist.
There is no breach to investigate, no incident to contain, no recovery to perform. The system does not need to be protected from itself, because it is not permitted to enter unauthorized states in the first place.
By enforcing authority at the state-transition level, DAIOS collapses cybersecurity from a sprawling ecosystem of tools into a single architectural decision: whether a machine is allowed to move at all.
That shift doesn’t make systems harder to attack.
It makes them impossible to compromise in the ways cybersecurity was built to address.
And that is why DAIOS doesn’t improve cybersecurity.
It replaces the need for it entirely.
From Cybersecurity to State Impossibility:
When Attacks Cannot Exist
Cybersecurity assumes that systems can be compromised and focuses on what to do after that compromise occurs. DAIOS challenges the assumption itself.
Most successful attacks do not rely on defeating defenses. They rely on the system accepting a state change that should never have been valid. Malware execution, unauthorized access, and lateral movement all depend on the same condition: the system is willing to represent an invalid state.
By enforcing deterministic authority before any state transition, the system no longer treats execution as default. A proposed action either satisfies the rules governing state change or it does not. When it does not, the transition never occurs and the state is never represented.
In that environment, the traditional cybersecurity lifecycle does not apply. There is nothing to detect because no invalid execution took place. There is nothing to contain because no unauthorized state propagated. There is nothing to recover from because no damage occurred.
The shift is not defensive. It is architectural.
When systems are no longer allowed to enter illegal states, attacks do not need to be blocked. They cannot exist.
Authority, and the End of Cybersecurity
as a Discipline
Cybersecurity emerged as a response to systems that were architected to tolerate error, misuse, and unintended behavior. It became an industry devoted to observation, remediation, and recovery precisely because machines were permitted to enter states they should never have reached.
DAIOS changes that premise at its root. By enforcing authority before execution, it removes the possibility of unauthorized state transitions altogether. The system does not require external protection from misuse because misuse is no longer a valid outcome the system can represent.
This is not a harder target or a more sophisticated defense. It is a different category of system, one in which the familiar vocabulary of exploits, breaches, and incident response no longer applies in the same way.
Authority enforced at the state-transition level does not advance cybersecurity incrementally. It renders the conditions that gave rise to cybersecurity unnecessary by design.
As machines become autonomous and decisions move beyond human oversight, that shift stops being philosophical. It becomes structural.
DAIOS does not sit alongside cybersecurity as another tool or framework. It marks the point at which cybersecurity, as a discipline built around post-execution control, reaches its natural conclusion.
TL;DR
DAIOS eliminates cybersecurity by preventing machines from entering unauthorized states in the first place. When authority is enforced at the state-transition level, attacks do not need to be detected or stopped because they cannot exist.